
- IT threat evolution Q1 2023
- IT threat evolution Q1 2023. Non-mobile statistics
- IT threat evolution Q1 2023. Mobile statistics
These statistics are based on detection verdicts of Kaspersky products received from users who consented to providing statistical data.
Quarterly figures
According to Kaspersky Security Network, in Q1 2023:
- 4,948,522 mobile malware, adware and riskware attacks were blocked.
- The most common threat to mobile devices was adware: 34.8% of all detected threats.
- 307,529 malicious installation packages were detected, of which:
- 57,601 packages were related to mobile banking Trojans,
- 1767 packages were mobile ransomware Trojans.
Quarterly highlights
Malware, adware and unwanted software attacks on mobile devices were down slightly year-on-year. Kaspersky mobile security systems thwarted a total of 4.9 million attacks in Q1 2023.
Number of attacks targeting users of Kaspersky mobile solutions, Q3 2021–Q1 2023 (download)
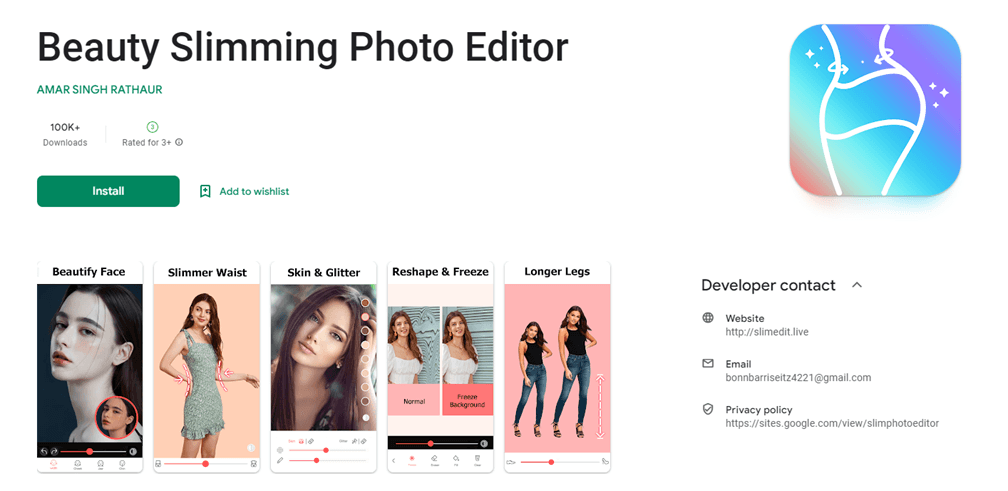
During the period in question, we detected several mobile photo editors on Google Play, which, besides their legitimate features, contained a dropper hidden inside a heavily obfuscated library. The dropper payload was designed to subscribe the user to paid services and intercept notifications.
We assigned our new find the verdict of Trojan.AndroidOS.Subscriber.aj and alerted Google Play, which then took down the malicious files. Kaspersky systems detect new files associated with this Trojan as Trojan.AndroidOS.Fleckpe.
Also in the first quarter, we came across what we designated as Trojan.AndroidOS.Bithief.f, a malicious modification of Skype that stole the victim’s cryptocurrency. The Trojan monitors the contents of the clipboard on the user’s computer and sends any crypto wallet addresses that it detects to the command-and-control server. The server responds with the hacker’s wallet address, so the malware substitutes that for the user’s address. And then inattentive users send their cryptocurrency to the wrong guys.
Mobile threat statistics
After a noticeable decrease in malicious installers in Q4 2022 due to reduced activity by Trojan-Dropper.AndroidOS.Ingopack, we observed a minor increase in new malware varieties.
Number of detected malicious installation packages, Q1 2022–Q1 2023 (download)
Distribution of detected mobile malware by type
Distribution of newly detected mobile malware by type, Q4 2022 and Q1 2023 (download)
Adware was back at the top of the rankings with 34.8%. The most widespread adware families in Q1 2023 were MobiDash (22.5%), HiddenAd (21.9%) and Adlo (12.4%).
Share of users attacked by a certain type of threat out of all attacked mobile users in Q4 2022 and Q1 2023 (download)
The share of users attacked by mobile Trojans increased in the first quarter, mostly due to the malware that we detect as Trojan.AndroidOS.Fakemoney.v and Trojan.AndroidOS.Adinstall.l. The former is a fake investment app that harvests victims’ payment details, and the latter, adware that comes pre-installed on certain devices, capable of downloading and running code (typically ads).
TOP 20 mobile malware programs
Note that the malware rankings below exclude riskware or PUAs, such as RiskTool or adware.
| Verdict | %* Q4 2022 | %* Q1 2023 | Difference in pp | Change in ranking | |
| 1 | DangerousObject.Multi.Generic | 16.52 | 13.27 | -3.24 | |
| 2 | Trojan-Spy.AndroidOS.Agent.acq | 4.29 | 8.60 | +4.31 | +5 |
| 3 | Trojan.AndroidOS.Boogr.gsh | 6.92 | 8.39 | +1.47 | +1 |
| 4 | Trojan.AndroidOS.Fakemoney.v | 1.13 | 7.48 | +6.35 | +19 |
| 5 | Trojan.AndroidOS.GriftHorse.l | 8.29 | 6.13 | -2.17 | -3 |
| 6 | Trojan.AndroidOS.Generic | 7.68 | 5.95 | -1.73 | -3 |
| 7 | Trojan-Dropper.AndroidOS.Hqwar.hd | 3.06 | 4.54 | +1.49 | +2 |
| 8 | Trojan-Downloader.AndroidOS.Agent.mh | 0.00 | 3.68 | +3.68 | |
| 9 | Trojan-Spy.AndroidOS.Agent.aas | 6.18 | 3.64 | -2.53 | -3 |
| 10 | DangerousObject.AndroidOS.GenericML | 2.37 | 3.46 | +1.10 | |
| 11 | Trojan.AndroidOS.Adinstall.l | 0.28 | 3.36 | +3.08 | |
| 12 | Trojan-Dropper.AndroidOS.Agent.sl | 3.50 | 2.10 | -1.40 | -4 |
| 13 | Trojan.AndroidOS.Fakemoney.u | 0.67 | 1.64 | +0.97 | +25 |
| 14 | Trojan-Banker.AndroidOS.Bian.h | 1.43 | 1.52 | +0.10 | +3 |
| 15 | Trojan-Dropper.AndroidOS.Hqwar.gen | 1.25 | 1.47 | +0.22 | +6 |
| 16 | Trojan-Downloader.AndroidOS.Agent.kx | 1.53 | 1.43 | -0.10 | -3 |
| 17 | Trojan-SMS.AndroidOS.Fakeapp.d | 6.43 | 1.32 | -5.11 | -12 |
| 18 | Trojan.AndroidOS.Piom.auar | 0.00 | 1.06 | +1.06 | |
| 19 | Trojan-Dropper.AndroidOS.Wroba.o | 1.51 | 1.03 | -0.47 | -4 |
| 20 | Trojan-Dropper.AndroidOS.Hqwar.gf | 0.14 | 0.98 | +0.84 |
* Unique users attacked by this malware as a percentage of all attacked users of Kaspersky mobile solutions.
DangerousObject.Multi.Generic (13.27%), the verdict we assign to miscellaneous unrelated malware that we detect with our cloud technology, topped the rankings as usual. This was followed by Trojan-Spy.AndroidOS.Agent.acq (8.60%), a malicious modification of WhatsApp that secretly monitors notifications the user receives.
Trojan.AndroidOS.Boogr.gsh (8.39%), a collective verdict for miscellaneous malware we detect with our machine learning technology, was in third place. This verdict is analogous to DangerousObject.AndroidOS.GenericML (3.46%), but unlike it, received through analysis of a similar file in the Kaspersky infrastructure.
Next were the previously mentioned fake investment app Trojan.AndroidOS.Fakemoney.v (7.48%) and the subscription Trojan described in many past reports — Trojan.AndroidOS.GriftHorse.l (6.13%).
Regional malware
This section describes mobile malware that mostly targets those who reside in certain countries.
| Verdict | Country* | %** |
| Trojan-Banker.AndroidOS.Banbra.aa | Brazil | 99.43 |
| Trojan-Spy.AndroidOS.SmsThief.td | Indonesia | 99.08 |
| Trojan-Banker.AndroidOS.Bray.n | Japan | 99.07 |
| Trojan-Banker.AndroidOS.Banbra.ac | Brazil | 98.85 |
| Trojan-Banker.AndroidOS.Agent.la | Turkey | 98.62 |
| Trojan.AndroidOS.Hiddapp.da | Iran | 97.82 |
| Trojan.AndroidOS.Hiddapp.bk | Iran | 96.95 |
| Trojan.AndroidOS.GriftHorse.ai | Kazakhstan | 96.26 |
| Trojan-Dropper.AndroidOS.Hqwar.hc | Turkey | 95.93 |
| Trojan.AndroidOS.FakeGram.a | Iran | 95.73 |
| Trojan-SMS.AndroidOS.Agent.adr | Iran | 95.07 |
| Trojan.AndroidOS.Hiddapp.bn | Iran | 95.01 |
| Trojan.AndroidOS.Piom.aiuj | Iran | 90.33 |
| Trojan-Banker.AndroidOS.Cebruser.san | Turkey | 88.28 |
| Trojan.AndroidOS.Hiddapp.cg | Iran | 88.25 |
| Backdoor.AndroidOS.Basdoor.c | Iran | 86.44 |
| Trojan-Dropper.AndroidOS.Wroba.o | Japan | 83.80 |
* Country where the malware was most active
* Unique users attacked by the malware in the indicated country as a percentage of all Kaspersky mobile security solution users attacked by the same malware
Members of the Banbra malware family continued to attack users in Brazil in Q1 2023. These are banking Trojans that abuse Accessibility features to interact with other applications installed on the device.
In Indonesia, users were exposed to spreading SmsThief.td SMS spies masquerading as public services, system apps or marketplaces.
Wroba banking Trojans, which we have covered several times, and the Bray mobile malware distributed under the guise of useful apps, such as call blockers, were busy in Japan.
Turkish users found themselves targeted by several banking Trojans, including the fairly primitive Agent.la and the well-known Cebruser. The Hqwar dropper operating in Turkey is also typically used to deliver various banking malware.
Users in Iran had to deal with hidden, hard-to-remove Hiddapp programs and the FakeGram family, third-party Telegram clients that automatically add users to channels they do not indent to join.
A variant of the GriftHorse subscription Trojan was mostly active in Kazakhstan. Focusing on users in a certain country is expected behavior for this Trojan family, as phishing messages used to lure the user into subscription to a fake service have to be localized.
Mobile banking Trojans
The number of banking Trojan installers began to increase again, exceeding 57,000 in Q1 2023.
Number of installation packages for mobile banking Trojans detected by Kaspersky, Q1 2022–Q1 2023 (download)
TOP 10 mobile bankers
| Verdict | %* Q4 2022 | %* Q1 2023 | Difference in pp | Change in ranking | |
| 1 | Trojan-Banker.AndroidOS.Bian.h | 29.90 | 30.81 | 0.91 | |
| 2 | Trojan-Banker.AndroidOS.Faketoken.pac | 6.31 | 10.15 | 3.84 | |
| 3 | Trojan-Banker.AndroidOS.Agent.eq | 4.59 | 5.51 | 0.92 | +1 |
| 4 | Trojan-Banker.AndroidOS.Agent.ep | 3.57 | 4.40 | 0.84 | +2 |
| 5 | Trojan-Banker.AndroidOS.Svpeng.q | 5.71 | 4.05 | -1.66 | -2 |
| 6 | Trojan-Banker.AndroidOS.Banbra.aa | 1.80 | 3.72 | 1.92 | +6 |
| 7 | Trojan-Banker.AndroidOS.Agent.la | 0.16 | 3.08 | 2.92 | +85 |
| 8 | Trojan-Banker.AndroidOS.Banbra.ac | 0.57 | 2.46 | 1.89 | +23 |
| 9 | Trojan-Banker.AndroidOS.Asacub.ce | 3.46 | 2.17 | -1.29 | -1 |
| 10 | Trojan-Banker.AndroidOS.Agent.cf | 1.63 | 1.91 | 0.28 | +5 |
* Unique users attacked by this malware as a percentage of all Kaspersky mobile security solution users who encountered banking threats.
Q1 2023 saw a noticeable year-on-year increase in activity by the aforementioned mobile malware Agent.la (3,08%) и Banbra (2,46%), which landed outside the TOP 10 in Q4 2022.
Mobile ransomware Trojans
The number of mobile ransomware programs remained low after dropping in 2022, apparently because the niche had ceased to be as profitable for scammers as it once had been.
Number of installation packages for mobile ransomware Trojans detected by Kaspersky, Q1 2022 — Q1 2023 (download)
TOP 10 mobile ransomware verdicts
| Verdict | %* Q4 2022 | %* Q1 2023 | Difference in pp | Change in ranking | |
| 1 | Trojan-Ransom.AndroidOS.Pigetrl.a | 54.61 | 62.22 | 7.60 | |
| 2 | Trojan-Ransom.AndroidOS.Small.as | 5.42 | 3.65 | -1.77 | |
| 3 | Trojan-Ransom.AndroidOS.Rkor.dl | 0.00 | 2.23 | 2.23 | |
| 4 | Trojan-Ransom.AndroidOS.Congur.y | 1.00 | 1.78 | 0.78 | +19 |
| 5 | Trojan-Ransom.AndroidOS.Agent.bw | 2.19 | 1.60 | -0.59 | -1 |
| 6 | Trojan-Ransom.AndroidOS.Fusob.h | 2.04 | 1.55 | -0.49 | +1 |
| 7 | Trojan-Ransom.AndroidOS.Rkor.pac | 1.19 | 1.50 | 0.32 | +9 |
| 8 | Trojan-Ransom.AndroidOS.Rkor.di | 0.62 | 1.46 | 0.84 | +30 |
| 9 | Trojan-Ransom.AndroidOS.Rkor.bi | 1.62 | 1.46 | -0.16 | +2 |
| 10 | Trojan-Ransom.AndroidOS.Small.o | 2.14 | 1.32 | -0.82 | -4 |
* Unique users attacked by the malware as a percentage of all Kaspersky mobile security solution users attacked by ransomware Trojans.
The distribution of mobile ransomware apps across quarters changed only insignificantly. Pigetrl (62.22%) still accounted for the lion’s share of threats, followed by Small.as (3.65%) and various modifications of Rkor.















IT threat evolution Q1 2023. Mobile statistics